Internet Censorship
Cyber censored: a thing of the past?
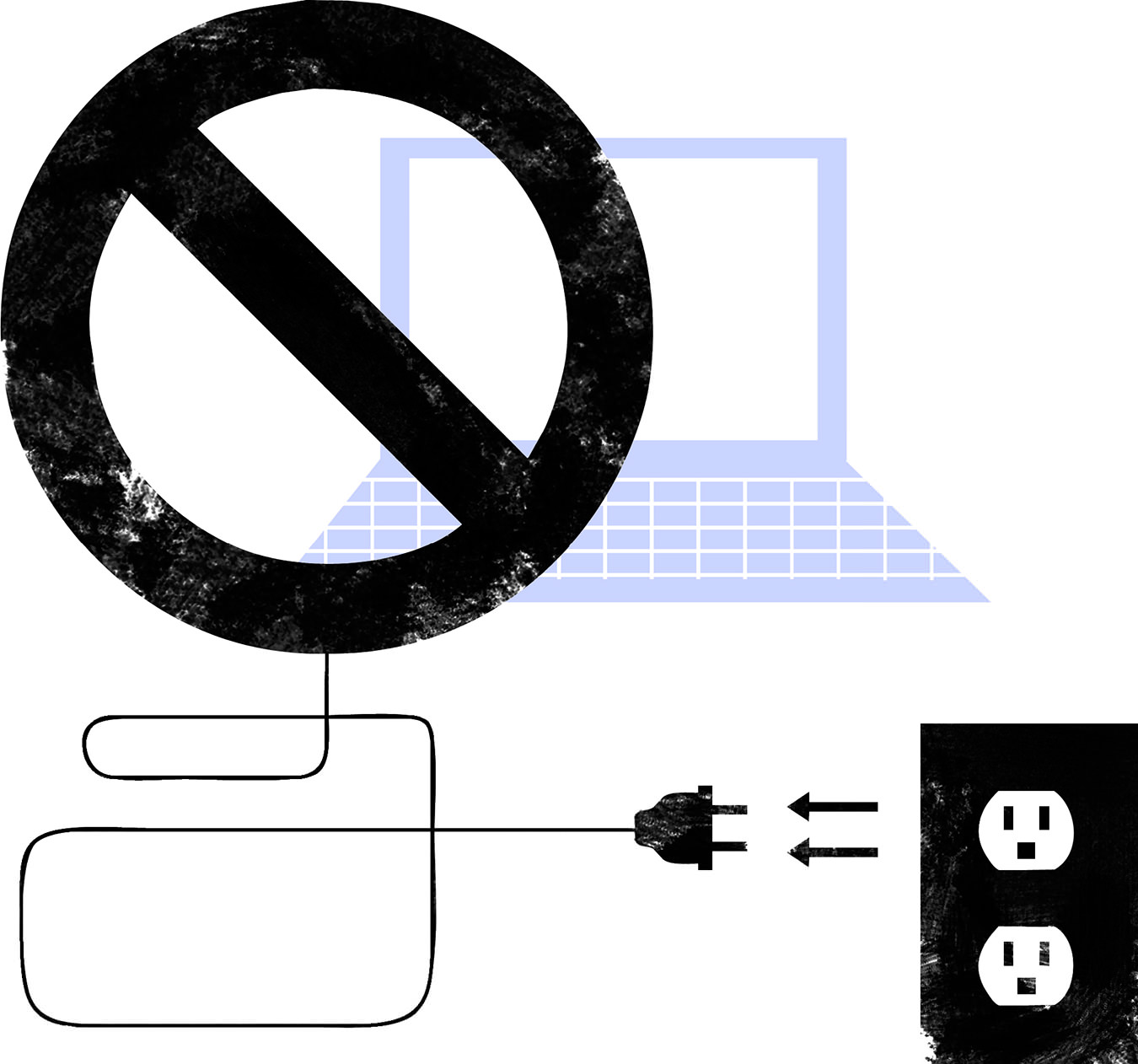
Illustration by Mark Reynolds.
It’s a dirty job, but someone’s gotta do it. Throughout history, censorship has been the first and most effective tool of dictators, both religious and secular. For the lackeys in charge of burning books, harassing journalists, and bestowing the occasional beat-down on poets, novelists, and playwrights, this has meant steady, if somewhat disreputable, employment.
Here in the digital age, however, the lackey profession has suffered something of a setback. The anything-goes scripto-anarchy of online culture has made electronic censorship a rather elusive goal. Short of pulling the plug on the entire Internet (and accepting the resultant economic consequences), it’s difficult for state-controlled agencies to monitor an ever-increasing mountain of user-generated blogs, articles, video, comments, and tweets. As fast as it’s taken down, it goes right back up.
Not that they don’t keep on trying. Back in September, a quartet of Central Asian autocracies (China, Russia, Tajikistan, and Uzbekistan) proposed that the United Nations adapt a “global code of conduct” for the World Wide Web and declare authority for all things Internet as the exclusive domain of the state. Up-and-coming economic powerhouses such as India, Brazil, and South Africa have also been clamouring for more control over Internet policy-making.
Over in the People’s Republic of China, the national Publicity Department (as pure an example of doublethink as ever you’ll find) has made Internet censorship job one. Social media sites that have become part of the Western zeitgeist—YouTube, Facebook, Twitter, et al.—are, officially, banned outright. Many Western news sites suffer the same fate, including our very own Radio Canada International. Same goes for all manner of counter-revolutionary blogs and chat rooms, and, perhaps surprisingly, some 60,000 porn sites. While tourists and business travellers can access most of the above in high-end hotel rooms, the sites remain verboten to most Chinese, locked behind the Great Firewall of China and monitored by an army of cybercensors more numerous than the fabled terracotta warriors.
It would be easy to dismiss such tactics as the desperate acts of politburos and tinpot dictators struggling to maintain their tenuous grip on power. But here in the developed world, there seem to be more than a few elected officials and state representatives musing about the need to police online speech. In May of this year, French President Nicolas Sarkozy convened a forum in Paris of the “e-G8” nations, making the case for more stringent regulation of the information superhighway. Across the channel, British Prime Minister David Cameron mused in Parliament about a limit or outright shutdown of Twitter, Facebook, and other social media sites as a way of preventing hoodlums from co-ordinating their efforts to pillage and burn during this past summer’s riots.
Now there comes a new weapon that may make such efforts to command and control moot. Developed jointly by researchers at both the University of Michigan and the University of Waterloo, Telex is a censor-busting program that may very well be the Manhattan Project of the war of online words—a doomsday weapon that will vanquish the foe utterly and send censors (of the electronic variety, at least) to the unemployment line. Researchers have already run a successful “proof of concept” test from Beijing, installing Telex software and streaming YouTube clips, unbeknownst to the People’s Republic.
Although the engineering is complex, the basic idea behind Telex is easy to understand. It doesn’t play the cat-and-mouse game of trying to find unblocked outside servers (called proxies) before government censors can shut the proxies down. Rather, it turns approved websites into proxies whether they like it or not. In essence, the entire Internet becomes a proxy server.
First, users install the Telex client application—presumably from a USB drive; perhaps from an encrypted website. The application attaches a special encrypted “tag” to the user request. Routers from participating Internet service providers (ISPs) outside the censoring country identify the Telex tag and implement anti-censorship services such as proxy servers or anonymity networks, through which users can then access blocked sites.
It’s this last part that makes Telex different—and somewhat problematic. Unlike other anti-censorship programs, Telex relies on the participation of ISPs located outside the censoring state to install Telex “stations” on the routes between approved and forbidden sites. These stations are the key to Telex’s success, working to recognize the unique encryption tag that Telex uses to encode the user’s request for censored content. The more participating ISPs, the more Telex stations installed. The more Telex stations installed, the more robust the system. The more robust the system, the more difficult it will be to take down.
Other than an altruistic desire to stick up for free speech, what incentive do ISPs have to participate in Telex’s efforts, particularly if such participation means sacrificing lucrative economic relationships with states that represent a good chunk of the world’s population? While companies such as Google have made their displeasure with censorship well known, others have been more than willing to co-operate with censors and state authorities as a price of doing business. Telex organizers admit that “incentive” may well have to come from federal authorities, perhaps the U.S. State Department or similar governmental agencies.
And that brings up more interesting questions: Is there legal prec-edent for such recruitment of corporations in the effort to spread free speech and democracy? Are Western governments willing to ante up in the efforts to stymie the censorship laws of sovereign states? Does such support constitute a new kind of cyberwarfare? If so, will it constitute an online casus belli, plunging nations into tit-for-tat hacking raids and denial-of-service assaults? We’ll have to wait and see.